Abstract
This article organizes the conceptual framework associated with the Q drops, viewed as a series of messages from President Trump and his team, into a structured set of testable hypotheses. Without evaluating the truth of the claims, it presents the underlying theory as a model of political control centered on a borderless syndicate, manufactured external threats, media influence, funding opacity, maritime concealment, demographic change, and crisis-driven governance. The purpose is to clarify the internal logic of the framework, present its major components in ordered form, and translate its themes into clearly defined propositions that could, in principle, be examined empirically
1. Introduction
The body of messages known as the “Q drops” presents information in a nonlinear and sometimes contradictory way. The authors of the drops themselves acknowledge that the material may include intentional disinformation. Yet when viewed together, the drops can be interpreted as internally consistent and capable of producing a coherent explanatory framework.
From this perspective, Q can be understood as a way for President Trump and his team to communicate complex ideas in coded form, allowing the public to research, interpret, and evaluate them over time.
This article does not evaluate whether the claims are true. Instead, it organizes the theory suggested by the drops and the hypotheses that come from it. Examples from the original formulation are preserved and labeled as potential illustrative cases. The post is inspired by the general direction of the Q framework, meaning that not every element necessarily appears directly in the drops themselves.
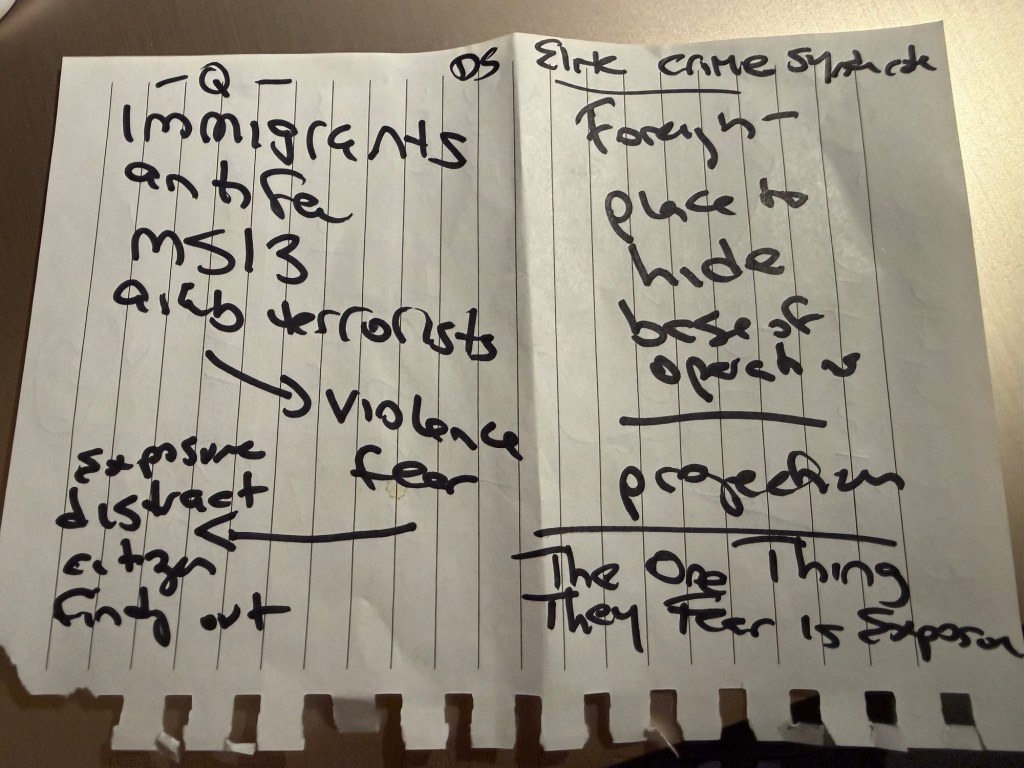
2. Core Theory: The Synthetic Adversary and the Subsidized Base
The central idea is that a borderless international syndicate, often described in the drops as the “Deep State,” maintains political control at home by creating or exaggerating outside threats.
These threats—sometimes called “The Other”—are used to justify limits on civil liberties and the expansion of government power.
Within this framework:
• Certain “Hostile Foreign Countries” serve as subsidized and non-transparent bases of operation.
• From these locations, illicit activities may occur outside normal law enforcement oversight.
These alleged activities include:
• Trafficking
• Bioweapons development
• Money laundering
At the same time, national sovereignty is weakened through open borders.
According to the theory, open borders serve two purposes:
• Import destabilizing threats into domestic society
• Expand the electoral base of a preferred political coalition
A media–entertainment complex is also described as helping protect this system. It does this by shaping narratives, avoiding discussion of corruption, and directing public attention toward approved targets.
3. Corollary Hypotheses for Empirical Testing
Hypothesis 1: Mass Brainwashing and Capture of Popular Culture
1.1 Premise
Control of cultural institutions and mass communication allows large-scale influence over how people think and feel.
1.2 Hypothesis
Media messaging, entertainment culture, marketing strategies, and psychological operations can blur the line between information and persuasion, creating a system of mass narrative control.
1.3 Mechanism
The theory suggests several layers of influence.
1.4 Cultural Capture
Entertainment and cultural institutions shape how people see politics and society.
Potential Examples
• Hollywood entertainment messaging
• Celebrity activism aligned with dominant political narratives
• Coverage patterns in major magazines and media outlets
• Persistent negative narrative amplification targeting Donald Trump
1.5 Marketing Culture and Narrative Engineering
Modern marketing techniques often blur the line between journalism, advertising, and persuasion.
Potential Examples
• Corporate media strategies that package political messaging through branding and emotional storytelling
• Political narratives spread through entertainment content and influencer culture
• Messaging designed to look organic while functioning as persuasion campaigns
1.6 Psychological Manipulation and Radicalization
The theory suggests that some individuals who commit violent acts may be influenced through psychological manipulation, radicalization, or pharmaceutical factors.
Potential Examples
• Disturbed or heavily medicated individuals who later commit mass shootings
• Radicalization inside online forums or digital echo chambers
• Individuals portrayed as isolated actors whose actions create national tragedy
In this interpretation, these individuals function as controlled or influenced actors whose crimes produce shock and fear.
1.7 Tragedy as Narrative Reset
Major violent events create emotional shock and dominate the news cycle.
Potential Example
• Mass tragedies receiving sustained national media coverage that pushes other stories out of the headlines
Within this framework, tragedy serves a strategic purpose: distracting the public from potential exposure of corruption or hidden networks.
Hypothesis 2: The Subsidized Hostility Loop (Military and Humanitarian Aid)
2.1 Premise
Foreign adversaries may sometimes function as indirectly supported actors through complex funding systems.
2.2 Hypothesis
Large military aid or humanitarian aid programs sent to conflict regions may include funding streams that are difficult to track and therefore vulnerable to diversion.
2.3 Mechanism
According to the theory:
• Diverted resources support foreign bases of operation
• These resources may help produce new threats such as militias or engineered pathogens
• These threats can later be used to justify expanded security powers at home
Potential Examples Referenced in the Framework
• Military aid related to the Ukraine–Russia conflict
• Humanitarian aid such as USAID funding in Somalia
• Aid programs directed toward Gaza
These examples are presented as cases where funding structures might lack transparency.
Hypothesis 3: The Maritime Shadow and Sovereign Exemptions
3.1 Premise
The ocean and remote islands can provide environments where law enforcement oversight is limited.
3.2 Hypothesis
Large trafficking operations may rely heavily on:
• Maritime shipping routes
• Private islands
3.3 Mechanism
The scale of global shipping and the complexity of international waters can provide:
• Concealment
• High transport capacity
• Enforcement gaps
Potential Examples Referenced in the Framework
• Maritime shipping networks used in global trade
• Private islands outside routine oversight
• Epstein Island as an example of a remote private property cited in trafficking discussions
These examples illustrate environments where such activities could theoretically occur.
Hypothesis 4: Demographic Dilution as Political Armor
4.1 Premise
Immigration policy can reshape the political landscape.
4.2 Hypothesis
Open border policies allow large-scale migration that can change electoral dynamics over time.
4.3 Mechanism
The theory suggests two effects:
• Increased instability through the entry of criminal or radical actors
• Expansion of the Democratic Party’s voter base through government benefits and social programs
Potential Examples Referenced in the Framework
• Policies allowing large numbers of migrants to enter with limited enforcement
• Government benefits or social programs used as incentives
• Political strategies aimed at converting new populations into long-term voters
Hypothesis 5: The Exposure–Event Correlation
5.1 Premise
The alleged syndicate fears public exposure more than physical confrontation.
5.2 Hypothesis
When exposure of foreign payrolls, trafficking networks, or maritime routes is about to occur, a sudden spike in dramatic violent events may follow.
These events may include:
• Mass shootings
• Terror attacks
• Vehicle ramming incidents
5.3 Mechanism
These incidents are often presented as acts of “lone wolves.”
Within this theory, they serve to reset the news cycle and redirect public attention away from possible revelations.
Actors that may be portrayed as destabilizing factors
• MS-13 gang members
• Antifa activists
• Arab terrorist networks
• Criminal illegal aliens
In this interpretation, these groups represent a mixed pool of potential perpetrators used to frame attacks in ways that reinforce public fear while shifting attention away from exposure risks.
4. Conclusion
In this framework, the alleged syndicate operates as a borderless network. Plans are created through international channels, and operations occur across multiple countries.
Its main enemy is populism, which seeks to return power to local citizens and expose the supposedly subsidized nature of foreign threats.
According to this theory, the system must continually maintain crisis conditions in order to survive.
These crises may include:
• War
• Terrorism
• Social conflict
• Recurring tragedy
Such events create fear and urgency. This atmosphere can justify expanded government power and discourage dissent.
The opposite conditions—peace, stability, prosperity, and genuine freedom—would allow citizens the time and clarity to think critically.
This includes:
• Political freedom
• Mental freedom
• The ability to live with stability and joy
In these calmer conditions, people might organize, investigate corruption, and expose hidden networks.
For this reason, the theory argues that the alleged “Deep State” has a structural incentive to avoid lasting peace and full civic freedom, because those conditions could allow citizens to recognize and stop the system.
5. Final Principle: WWG1WGA
The phrase WWG1WGA (“Where We Go One, We Go All”), popularized by the movie White Squall, is often presented as the final summary of the theory.
It represents the moment when citizens move beyond the distractions of manufactured enemies and recognize that their individual futures are tied to the fate of the nation as a whole.
Within this framework:
• The syndicate survives when society remains divided
• Division is fueled by fear and “Mirror Projection”—accusing opponents of the same crimes
When citizens recognize that an attack on the liberties of one is an attack on the sovereignty of all, the theory argues that the system loses its power.
Unity then shifts attention away from manufactured crises—whether a virus, a gang, or a foreign threat—and toward a shared mission of restoring transparent and accountable government.
In this vision, people move past the media-entertainment shield, help one another reclaim their nations, and live side-by-side in a restored and transparent society.
Written with the help of AI.
You must be logged in to post a comment.