This article examines how the combination of military and intelligence officials, along with certain journalists and media figures, forms an ecosystem of disinformation and propaganda—where informal approvals and inside‑sounding claims are recklessly, and sometimes fraudulently, used to make conspiracy theories look like official intelligence findings.
1. Mitch Snow’s Revelation: The “Informal Vetting” Claim
The most consequential new development comes from the March 21, 2026, Teresa Better Life interview with self‑described whistleblower Mitch Snow (Snow, 2026). In that conversation, Snow described a December 2025 episode that reveals the core mechanism of the “White Hat” ecosystem: informal vetting treated as official validation.
Snow’s account is strikingly explicit:
- “Yeah, we had a 15‑minute conversation… all he had to do was see records. I gave him all the records; I gave him so many records.” (Snow, 2026)
- “He said, ‘Stop, you’re done. You check out. You’re good with this station. Move forward. Good luck on Candace.’” (Snow, 2026)
- “Joe Kent… he can take the records, go look it up, dial stuff in. He knows more about my records than I do. He has access to it straight up.” (Snow, 2026)
- “Seems like a lot of ‘white hats’ who are in the know trust him.” (Snow, 2026)
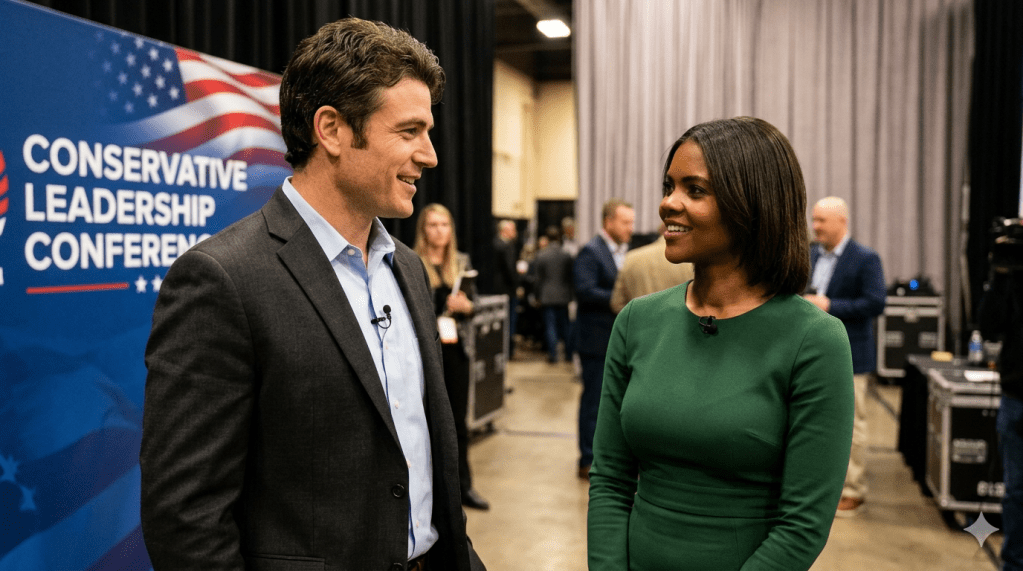
Whether Snow’s interpretation is ultimately accurate or self‑serving, the episode is sociologically significant. An informal interaction with a sitting Director of the National Counterterrorism Center (NCTC) is being framed—not by the IC but by supporters—as institutional approval. That is the laundering process in real time. The investigative leads that first exposed this pattern were highlighted by digital commentators Cinema Shogun (@cinemashogun) and Laura Loomer (@lauraloomer), who connected the Snow‑Kent‑Owens thread to larger concerns about Signal‑based leaks and informal vetting (Cinema Shogun, 2026; Loomer, 2026).
2. The Catalyzing Narrative: Charlie Kirk, Erika Kirk, and the “Fort Huachuca” Theory
To see how that laundering is deployed, one must return to the aftermath of Charlie Kirk’s September 2025 killing (Assassination of Charlie Kirk, 2026). In the vacuum of grief and shock, the “Fort Huachuca” theory gained traction within certain media circles. In that narrative, Erika Kirk is alleged to be collusive with “deep‑state” actors in the planning or aftermath of the murder (Bajaj, 2025; CNN, 2025).
This report does not attempt to prove or disprove the underlying conspiracy claim. What is analytically important is the discursive ecosystem that emerged around it. The theory was not merely circulated; it was repeatedly presented as if it had been vetted by figures with national‑security standing, despite the absence of any formal IC finding (Assassination of Charlie Kirk, 2026; CNN, 2025). See below:
“During a livestream on X on Monday, Candace Owens said she did not bring up Fort Huachuca in her private talk with Erika Kirk because she was still checking details. She said, ‘During that meeting, I did not bring up the Fort Huachuca thing because I first and foremost needed to continue vetting various aspects of it…’” https://www.msn.com/en-in/news/world/i-was-just-going-to-candace-owens-reveals-why-she-avoided-fort-huachuca-claims-during-private-erika-kirk-meeting/ar-AA1TiZ2X
When informal approval from a high‑ranked figure is attached to such a narrative, it ceases to be just a rumor. It becomes a scripted rumor: one designed to exploit the gap between public perception and institutional process.
3. Signal Gate: The Precedent for Recklessness
The Snow episode is best understood in light of the March 2025 Signal Gate scandal, which is already a documented breach of protocol. Senior Trump‑administration officials, including Pentagon and national‑security aides, used the unsecured messaging app Signal to coordinate sensitive military operations related to Yemen, sharing details such as strike timing, weapon types, and target windows (The Atlantic, 2025; Politico, 2025; CNBC, 2025). A journalist, The Atlantic’s Jeffrey Goldberg, was accidentally included in one of the threads, causing the leak to erupt into public view (The Atlantic, 2025). The “Signal group” exposed the administration’s use of an unsecure platform for real‑time war‑planning, and the incident has since become a case study in norm erosion at the highest levels (The Atlantic, 2025; Fortune, 2025).
Signal Gate matters here because it shows that formal protocols are not immovable. When officials treat secure channels as optional, they open the door to precisely the kind of informal, off‑the‑books communication that Snow describes. The Snow‑Kent‑Owens axis, whether or not it is equally explosive, develops within the same cultural frame: the belief that insider channels are discretionary, not binding. The broader implications of Signal‑based war‑planning leaks have been widely analyzed in legal and policy commentary (Price & Jarvis, 2024).
4. Authority Laundering and the “White Hat” Veneer
The deeper structural problem is authority laundering—the use of official or quasi‑official status to convert personal opinion into perceived institutional truth. Joe Kent, LTG Mike Flynn, and similar figures are not unique cases. They are emblematic of a pattern in which the “military‑intelligence” label acts as a proxy for credibility (New York Times, 2025; Clark, 2022).
The “White Hat” ecosystem relies on two overlapping mechanisms (Clark, 2_rsp style):
- Military/Veteran Immunity: By invoking titles like “LTG” or “National Counterterrorism Center Director,” these figures create a sense of moral immunity. To question the claim is to question the institution itself.
- Narrative Capture: Once the “vetting” or “green light” label is attached, the story is no longer a conspiracy theory. It is a “leaked” or “insider” narrative, repeated across podcasts, talk shows, and social platforms.
This is the authority trap: the speaker’s status performs the work of proof, and the audience scans the claim for confirmation rather than verification.
5. The Information Laundering Pipeline
- The process begins when a source (often a former or current official) offers a “nod,” an informal private record review, or an ambiguous endorsement of a narrative. This source provides the “White Hat” veneer—the appearance of insider authority without the accountability of an official report.
- Media figures are always looking for “scoops” that align with their predetermined bias. So they take the source’s informal conversation and frame it as “insider knowledge” or “leaked” information. While they may not explicitly say the story was “vetted” in a legal sense, they present it as valid information; they become reckless when they believe that the story has the blessing of someone from the military and/or intelligence community.
- The story is broadcast to the audience, which is already primed to trust the media figure. They interpret the “insider” framing as official corroboration. Because it sounds like it has official backing, the story gains a level of legitimacy that allows it to spread faster than any factual rebuttal could travel.
- Once the audience accepts the “laundered” truth, the narrative is often weaponized. This final stage involves: moving from “insider info” to targeting specific groups, using the theory to justify prejudice.
6. Oversight Failure and the ODNI Vacuum
The persistence of these behaviors points to a systemic oversight vacuum within the Office of the Director of National Intelligence (ODNI). The ODNI is supposed to enforce discipline, prevent politicization, and protect the integrity of intelligence operations. Yet when senior officials are seen as bending or breaking rules without consequence—Signal Gate, unsecured messaging, and now the Snow‑Kent‑Owens axis—the gravitational pull is toward further normalization (Assassination of Charlie Kirk, 2026; CBS News, 2026).
Where there is weak disciplinary follow‑through, the message sent is clear: protocol exists only where it is politically inconvenient. That is not a security culture. It is a culture of privilege.
7. Radicalization and Antisemitic Framing
The most dangerous extension of the laundering machine appears in the rhetoric around the “Israel lobby” and “Synagogue of Satan” framing, as well as the baseless claims circulated against Erika Kirk (Bajaj, 2025; CNN, 2025). Antisemitic tropes are not incidental to this ecosystem. They are instrumental. They help convert abstract policy critique into a narrative of “treasonous” or “subversive” elites. The “Fort Huachuca” theory, allegedly “vetted” by Kent’s informal nod and then broadcast through media allies, becomes a tool for targeted character assassination. The laundering process supplies the credibility cover that allows the theory to circulate without bearing the full evidentiary burden.
8. Legal and Investigatory Questions
This conduct raises serious legal and institutional questions, even if the record remains incomplete.
A. Government Officials (Joe Kent, Mike Flynn, etc.)
- Hatch Act (5 U.S.C. §§ 7321–7326): If an official used their position to provide informal vetting for a partisan media figure, that could amount to a misuse of official authority (U.S. Office of Special Counsel, 2014).
- Espionage Act (18 U.S.C. § 793): If national‑defense information was shared through unsecured channels, or if gross negligence occurred in handling sensitive data, legal exposure increases (U.S. National Counterterrorism Center, 2014).
- Privacy Act and Records Obligations: If official records or access were used to support private media narratives, that could trigger ethics and record‑keeping violations.
- UCMJ and post‑employment norms: For retired officers, the use of “LTG” status to advance unsubstantiated political narratives may invite scrutiny for contemptuous or inciting speech (New York Times, 2025).
B. Media Figures (Candace Owens, Tucker Carlson, etc.)
- Actual Malice in Defamation: The “vetted by the NCTC” narrative, if used to justify the Erika Kirk smears, raises questions of reckless disregard for the truth. Claiming institutional validation where none exists is a classic red flag (U.S. Office of Special Counsel, 2014; Price & Jarvis, 2024).
- Government investigatory power: The DOJ or congressional committees can subpoena communications logs, metadata, and private messaging records to ascertain the frequency, nature, and content of contacts between officials and media “magnifiers.”
9. Reform Proposals for the ODNI
To prevent the laundering machine from becoming a permanent feature of the national‑security discourse, the ODNI and related bodies must act (U.S. National Counterterrorism Center, 2014; U.S. Office of Special Counsel, 2014):
- Prohibit informal vetting by sitting officials for private media or political narratives, even if no formal database query occurs.
- Ban the use of ephemeral messaging platforms (e.g., Signal, TeleMessage) for any operational or national‑security decision‑making, and require “always‑on” logging for senior‑official communications.
- Strengthen benefit accountability: Former officials who exploit their military or intelligence veneer to advance narratives that endanger national security or harm private citizens could face forfeiture of federal benefits.
- Clarify ethics rules: Explicitly codify that the use of official status to lend credibility to conspiracy theories is incompatible with public‑service obligations.
- Expand oversight: The ODNI Inspector General, the House and Senate Intelligence Committees, and the Office of Special Counsel must all have standing authority to investigate such informal coordination.
10. Conclusion
The “Joe Kent, Mitch Snow, & the White Hat Laundry Machine” episode is not merely a scandal. It is a case study in how prestige asymmetry can be weaponized within the national‑security discourse. When an informal nod from a national‑security official is treated as a formal endorsement, the line between institution and ideology collapses. The laundering machine is not accidental. It is a product of weak norms, weak enforcement, and weak public scrutiny. The question that remains is not just whether this pattern is happening, but whether the institutional response will match its gravity—or whether, once again, the rules will be treated as optional for those who already hold the authority.
Bibliography
AI, Y. (2025, September 11). AI fuels false claims after Charlie Kirk’s death, CBS News analysis finds. CBS News. https://www.cbsnews.com/news/ai-false-claims-charlie-kirk-death/
Assassination of Charlie Kirk. (2026, March 22). In Wikipedia. https://en.wikipedia.org/wiki/Assassination_of_Charlie_Kirk
Bajaj, Y. N. (2025, December 25). Candace Owens vs Alex Jones heats up over Mitch Snow, Fort Huachuca theory after Erika Kirk allegation. Hindustan Times. https://www.hindustantimes.com/world-news/us-news/candace-owens-vs-alex-jones-heats-up-over-mitch-snow-fort-huachuca-theory-after-erika-kirk-charlie-kirk-allegation-101766622783111.html
CBS News. (2026, March 19). Joe Kent, ex‑Trump counterterrorism chief who resigned over Iran war, under FBI investigation for alleged leaks. CBS News. https://www.cbsnews.com/news/joe-kent-national-counterterrorism-center-director-fbi-investigation-leaks/
CBS News. (2026, March 19). Gabbard, intel officials face more sharp questions on Iran war at House hearing. CBS News. https://www.cbsnews.com/live-updates/tulsi-gabbard-house-intelligence-committee-worldwide-threats-hearing/
Clark, K. M. (2022). Meme wars as socially situated learning: Learning in online communities of hate, conspiracy, and insurgency. Midwest Social Sciences Journal, 28(1), 30–64. https://scholar.valpo.edu/mssj
CNBC. (2025, May 5). Messaging app used by Trump official suspends operations. CNBC. https://www.cnbc.com/2025/05/05/signal-telemessage-hack-trump-waltz.html
Cinema Shogun. (2026, March 21). HOLY SHT 🤯 Mitch Snow just MESSED UP big time. He accidentally revealed that Joe Kent has been in communication with him and Candace Owens behind the scenes… [Post]. X. https://x.com/cinemashogun/status/2035523701802762411
CNN. (2025, September 20). Fact check: Debunking the Charlie Kirk murder conspiracy theories. CNN. https://www.cnn.com/2025/09/20/politics/fact-check-charlie-kirk-murder
Fortune. (2025, March 24). Trump administration’s use of disappearing Signal messages to manage military strikes not allowed under records law expert. Fortune. https://fortune.com/2025/03/25/trump-administrations-signal-military-strikes-not-allowed-under-record-law-expert/
Loomer, L. (2026, March 22). Wow. So let me dissect this. Has @joekent16jan19 been using his position as the Director of the National Counterterrorism center to feed @RealCandaceO’s lies to push their deranged Charlie Kirk conspiracy theories? [Post]. X. https://x.com/lauraloomer/status/2035651869356237310
Money, G. (2025, March 24). Trump administration accidentally texted me its war plans. The Atlantic. https://www.theatlantic.com/politics/archive/2025/03/trump-administration-accidentally-texted-me-its-war-plans/682151/
Politico. (2025, March 24). 5 revelations from the Trump administration’s war plan texts. Politico. https://www.politico.com/news/2025/03/24/5-revelations-national-security-war-plans-texts-00245721
Price, N., & Jarvis, J. (2024). Conspiracy jurisdiction. Stanford Law Review, 76, 403–480.
Shannon M. Kent. (2026, March 20). In Wikipedia. https://en.wikipedia.org/wiki/Shannon_M._Kent
Snow, M. (2026, March 21). LIVE with Mitch Snow: Joe Kent vetted Mitch Snow for Candace Owens [Video]. YouTube. https://www.youtube.com/live/krtQE0wXwUw
U.S. National Counterterrorism Center. (2014, February). Overview of the baseline safeguard protections under NCTC’s 2012 Attorney General Guidelines. DNI.gov.
U.S. Office of Special Counsel. (2014, September). A Guide to the Hatch Act for federal employees. OSC.gov.
Disclaimer: The views and opinions expressed in this report are mine alone and are presented in my personal capacity. This work was produced on personal time, using personal devices, and on private premises. It does not represent the official policy, position, or endorsement of any government agency, military entity, or private employer. Written with the help of AI. AI generated image.
You must be logged in to post a comment.